The security of a live event is only as strong as its access control system. Paper wristbands can be duplicated at any print shop. QR codes can be photographed and shared. Physical ID checks at scale are slow and inconsistent. RFID credentials eliminate each of these vulnerabilities simultaneously.
RFID wristbands and badges are now the access control standard for events across Saudi Arabia — from international sporting events and government conferences to music festivals and corporate summits. This guide covers the complete security architecture: how RFID credentials work, how zones are configured, how counterfeiting is prevented, and how real-time monitoring gives security teams operational intelligence they could not achieve with any other credential type.
Whether you are securing a 500-person corporate event or a 50,000-person festival, the principles are the same — only the scale changes.
RFID Security Performance Benchmarks
99.9%
Access Accuracy
<300ms
Authentication Time
0
Duplication Risk
100%
Audit Trail
RFID Security Fundamentals
RFID event security operates through a combination of hardware encryption, real-time database authentication, and physical tamper-evidence. Each element addresses a different attack vector — together they create a security layer that is significantly more robust than any paper or QR-based alternative.
AES-128 Encryption
Every RFID credential issued by StampIQ uses AES-128 encryption at the chip level. The credential data is never transmitted in plain text — each read event uses a challenge-response protocol where the gate reader and the chip mutually authenticate before any data is exchanged.
Unique Credential IDs
Each RFID chip is assigned a unique event-specific credential ID at the time of encoding. The ID is meaningless outside the event's access control system and cannot be transferred to another chip — even if the physical wristband or badge is replicated exactly.
Real-Time Database Sync
All gate readers sync with the central credential database continuously. A wristband that is voided at 10:32am is rejected at all gates by 10:32:01am — there is no window of opportunity to use a cancelled credential.
Tamper-Evident Design
RFID wristbands use tamper-evident closures — once fitted, removal destroys the wristband. RFID badges use lanyards with holographic overlaminates that show visible evidence of tampering if the chip is attacked or the card surface is modified.
Multi-Gate Validation
For high-security events, StampIQ deploys layered gate validation — a credential must authenticate successfully at a primary gate before it is even presented to secondary zone gates. This prevents credential spoofing at internal access points.
Offline Authentication Fallback
In the rare event of network connectivity loss, RFID readers operate in offline mode using a locally cached credential list. The list is refreshed every 60 seconds during normal operation, ensuring offline mode uses the most recent data available.
Wristbands vs Badges: Choosing the Right Credential
The choice between RFID wristbands and RFID badges is primarily driven by event type and the need for visible credential display. Both formats use the same chip technology and integrate with the same access control system.
RFID Wristbands — Best For
- Concerts and music festivals
- Sports events and tournaments
- Multi-day outdoor events
- Events where credential sharing must be prevented
- Cashless payment integration events
RFID Badges — Best For
- Conferences and trade shows
- Government and ministerial events
- Corporate summits and forums
- Events requiring visible name display
- Media and press accreditation
Hybrid deployments: Some events use both formats simultaneously — RFID badges for accredited professionals (media, staff, speakers) and RFID wristbands for general admission audiences. StampIQ manages both credential types within the same access control system with no additional configuration complexity.
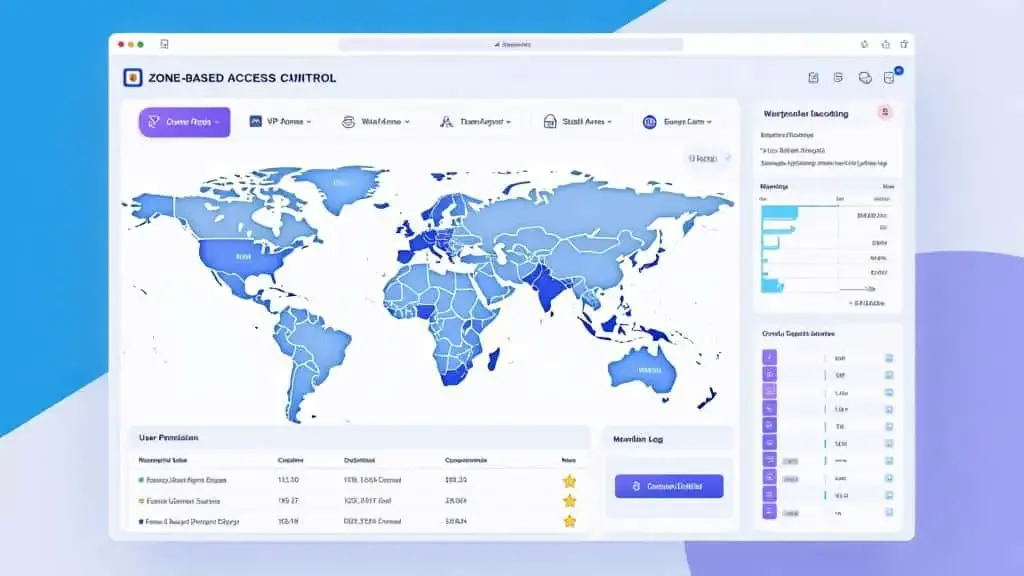
Zone-Based Access Control
Zone-based access is the core security architecture of RFID event management. Each attendee's credential is encoded with a specific set of zone permissions — and every gate in the venue verifies those permissions in real time before granting or denying entry.
All valid credentials. Main event areas, public spaces, general exhibition halls.
Premium credential class. Exclusive lounges, priority areas, VIP viewing positions.
Press credentials. Media centres, press conference rooms, designated filming positions.
Staff and production credentials. Technical areas, backstage, equipment zones.
Anti-Counterfeiting Features
Counterfeit event credentials are a persistent problem for high-demand events. RFID eliminates the most common counterfeiting methods — but the security is only as strong as the chip encryption used.
StampIQ Anti-Counterfeiting Stack
- MIFARE DESFire EV3 chips with AES-128 — resistant to all known cloning attacks
- Mutual authentication protocol — gate and chip verify each other before any data exchange
- Event-specific credential keys — credentials are invalid outside the event system
- Holographic overlaminates on badges — visible tamper evidence if chip is attacked
- Tamper-evident wristband closures — removal destroys the credential irreversibly
- Real-time database check — voided credentials rejected system-wide within 1 second
Real-Time Monitoring
Real-time monitoring converts RFID access data into operational security intelligence. Every gate scan generates a timestamped event — and those events, aggregated across all gates, create a live picture of exactly who is where in the venue at any moment.
Live Credential Status
See all active, voided, and pending credentials in real time.
Denied Access Alerts
Instant notification when credentials are rejected — with gate location and timestamp.
Zone Occupancy
Live headcount per zone — compare against capacity limits and trigger alerts automatically.
Anomaly Detection
AI flags unusual patterns: duplicate scans, out-of-sequence entries, high denial rates at a gate.
Security Protocols
Technology alone does not create a secure event. These six operational protocols, applied alongside StampIQ's RFID infrastructure, constitute a complete event security framework for Saudi Arabia events.
Pre-Event Credential Audit
24 hours before the event, run a full credential audit: verify the total number of issued credentials against the registered attendee list, confirm all voided credentials are deactivated in the system, and test a sample of credentials at each gate type to confirm zone permissions are correctly encoded.
Gate Configuration Check
Each RFID reader must be configured with the correct zone permission set before the event opens. A gate reader set to the wrong zone will allow or deny access incorrectly — a configuration check 2 hours before door-open catches this before it affects attendees.
Staff Briefing on Escalation
All gate staff must know the escalation protocol for: denied access attempts, damaged credentials, suspected gate crashes, and lost wristbands. Clear escalation paths prevent on-the-spot decisions that create security inconsistencies.
Live Monitoring Assignment
Designate a security operations lead responsible for monitoring the live dashboard throughout the event. This person watches for anomaly alerts, crowd density warnings, and denied access clusters that may indicate a security issue at a specific gate.
Void & Replace Protocol
When a credential is reported lost or stolen, it must be voided immediately — not at the end of the day. StampIQ's void function deactivates the credential system-wide in under 2 seconds. A replacement credential is issued with a new unique ID, and the old credential is permanently deactivated.
Post-Event Security Review
Review the access log for anomalies: credentials used outside their registered session windows, unusual denied access clusters, credentials that attempted access to zones above their permission level. This review informs security planning for the next event.
Frequently Asked Questions
Secure Your Next Event with RFID Technology
StampIQ provides complete RFID wristband and badge security systems — with AES-128 encryption, real-time monitoring, and full audit trails — for events across Saudi Arabia and the GCC.
Get a Security Demo